TLDR
OPC-UA (IEC 62541) is the industrial automation protocol that lets PLCs, sensors, MES systems, and edge AI inference servers exchange data with consistent semantics, built-in security, and platform independence. For edge AI, OPC-UA solves the "context problem": raw signals become typed, addressable objects an inference engine can reason about. This guide explains how OPC-UA works, why it has become the default integration layer for converged IT/OT deployments, and which Neousys edge AI computers are best suited to run an OPC-UA client, server, or PubSub broker on the plant floor.
Overview
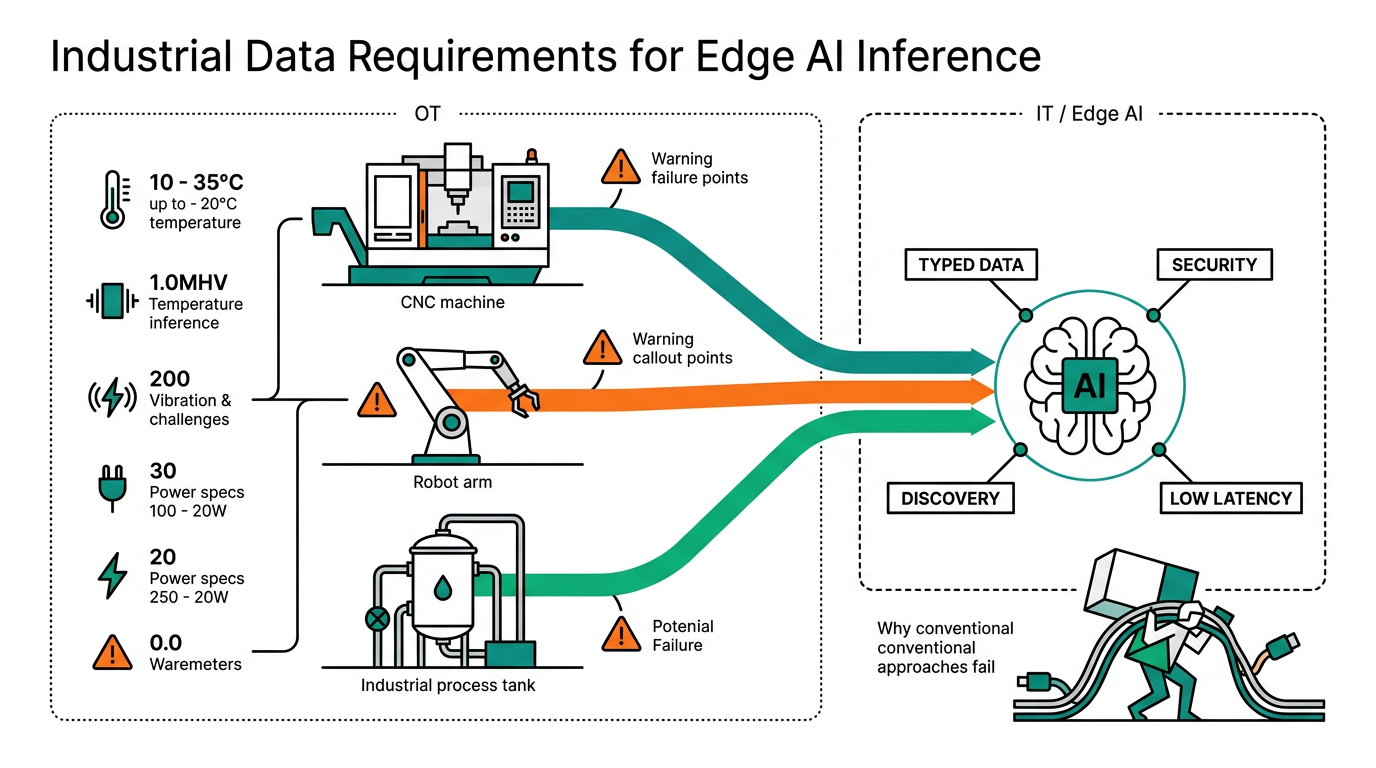
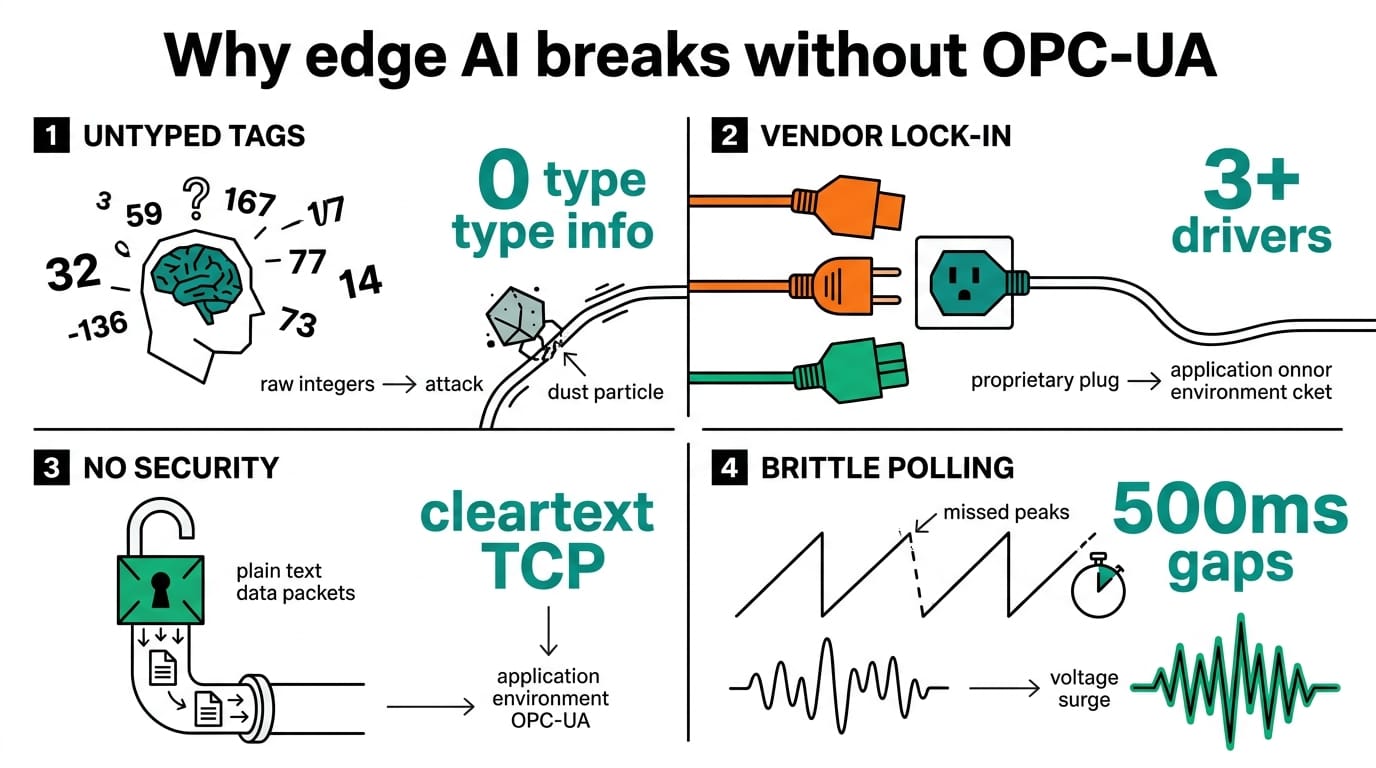
Walk into any modern factory and you'll find a stack of protocols on the wire: Modbus TCP, EtherNet/IP, PROFINET, MQTT, CIP. Each one solves a slice of the problem, but none of them carry the meaning of the data — a tag named `HR40001` could be a temperature, a torque value, or a part count, and the consuming application has to be told which. OPC-UA fixes that by combining a transport, an information model, and a security layer into one specification.
That matters more for edge AI than for traditional SCADA. An inference model trained on "spindle vibration RMS over 60 seconds, sampled at 10 kHz, in mm/s" needs every one of those qualifiers preserved end to end. OPC-UA is how that context survives the trip from sensor to GPU. In our machine vision system design guide we treated the camera as the data source; here we look at the protocol layer that ties cameras, PLCs, and AI nodes into one coherent graph. For broader context on where this fits in the 2026–2030 manufacturing landscape, see our Edge AI in Manufacturing outlook.
What It Is
OPC-UA is the successor to the original Microsoft-DCOM-based OPC Classic. It is a service-oriented protocol maintained by the OPC Foundation and standardized as IEC 62541. Three traits distinguish it from older industrial protocols:
- Transport-independent. It runs over TCP (`opc.tcp://`), HTTPS, and increasingly MQTT or UDP multicast (PubSub).
- Object-oriented information model. Data is exposed as nodes with types, references, and metadata — not flat register addresses.
- Security is mandatory, not bolted on. X.509 certificates, message signing, and per-user role mapping are part of the base spec.
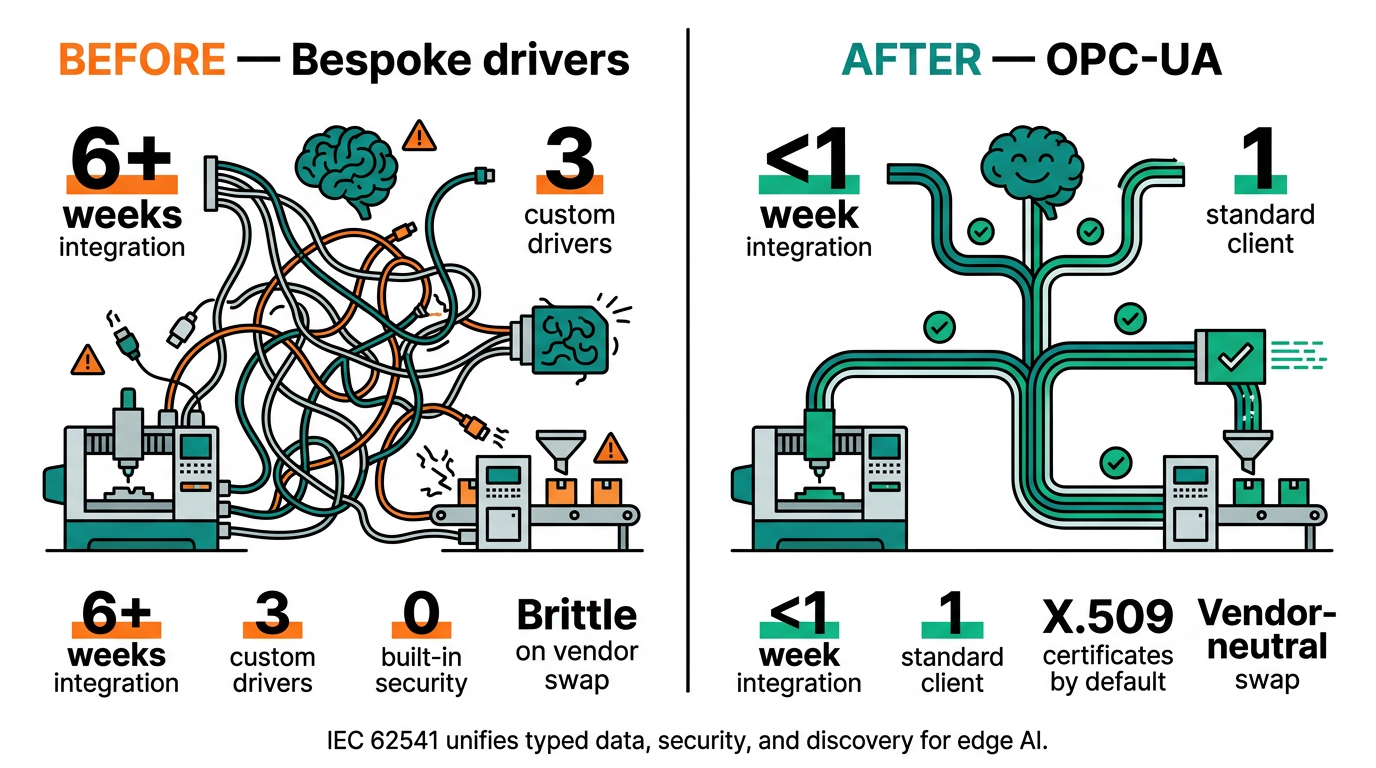
This is what allows a single OPC-UA endpoint on a Nuvo-11000 edge controller to publish a 5,000-tag plant model that any compliant client — historian, MES, AI inference service — can browse and subscribe to without a custom driver.
How It Works
An OPC-UA session has four moving parts: a server (the data source), a client (the consumer), a session/subscription pair (the conversation), and an address space (the typed object graph). The table below maps the protocol flow against the artifacts an integrator actually deals with.
For protocol-side context, see our explainer on MQTT vs Modbus TCP for edge AI pipelines.
| Stage | What Happens | Edge AI Artifact |
|---|---|---|
| Discovery | Client queries server endpoint URL, retrieves supported security policies | `opc.tcp://nuvo-11000.plant.local:4840` endpoint published by edge node |
| Secure Channel | TLS-style handshake using X.509 certs; selects Sign+Encrypt policy | Certificate trust list managed on the Nuvo-11000 TPM |
| Session | Authenticated user/role binding; negotiates session timeout | Inference service authenticates as `ai-reader` role |
| Browse | Client walks the address space to find nodes of interest | AI pipeline locates `Plant/Line03/Spindle/VibrationRMS` |
| Subscription | Client requests change-notifications at a sampling interval | 100 ms publishing interval feeds the GPU on Nuvo-10108GC |
| PubSub (optional) | Server publishes datasets over MQTT/UDP for many-to-many delivery | Same data fans out to historian, dashboard, and inference node |
The key idea: the AI workload subscribes to named, typed values. There is no magic register decoding in the inference container — the OPC-UA stack delivers a `Double` named `VibrationRMS` with units, a deadband, and a timestamp.
Why Edge AI Needs It
Three reasons OPC-UA has become the default integration layer for industrial AI deployments:
- Context preservation. Models drift when the meaning of a feature changes. OPC-UA's information model gives every signal a stable identifier and unit, so a model trained six months ago still gets the right input today.
- Bidirectional control. Subscribing to data is the easy half. Writing inference results back as setpoints — for closed-loop control, for example pacing a conveyor based on a defect-rate prediction — requires a protocol that supports authenticated writes. OPC-UA does; MQTT alone does not.
- Determinism for safety-adjacent loops. OPC-UA over TSN gives bounded latency, which is what makes it acceptable for soft-real-time AI loops sitting next to PLCs.
For a deeper look at how protocol choice affects latency budgets in production AI systems, see our case study on acoustic leak detection on a refinery pipeline, where OPC-UA carried both the inference inputs and the alarm acknowledgements.
Which Products Support It
Every Neousys edge platform Neteon ships can run an OPC-UA stack — open62541, Eclipse Milo, or a vendor SDK such as Unified Automation. The deployment role drives the hardware choice.
| Role | Recommended Platform | Why |
|---|---|---|
| OPC-UA server (plant aggregator) | Nuvo-11000 | Intel Core Ultra, TPM 2.0, 8 GbE ports — handles 50K+ tags with TLS |
| OPC-UA client + AI inference | Nuvo-10108GC | RTX-class GPU runs the model while the OPC-UA client subscribes to the feed |
| Edge gateway / protocol bridge | Nuvo-10000 | Modular slots for fieldbus cards, ideal for translating Modbus/PROFINET into OPC-UA |
| Network underlay | PLANET IGS-10020MT | Managed industrial switch with QoS and IGMP snooping for OPC-UA PubSub multicast |
A practical pattern for greenfield deployments: a Nuvo-10000 at each line aggregates legacy PLC traffic and re-exposes it as OPC-UA; a single Nuvo-11000 at the cell level acts as the master server; Nuvo-10108GC nodes subscribe selectively for inference workloads.
Related Products
For the layer underneath OPC-UA — the Ethernet timing that lets the protocol meet a control deadline — see our plain-English guide to TSN.
Conclusion
OPC-UA is not glamorous — it's plumbing. But it is the plumbing that makes edge AI deployments survive a plant audit, an MES upgrade, and the next model retraining cycle. Treating it as a first-class part of the architecture, rather than a last-mile adapter, is what separates pilots that scale from pilots that get rebuilt.
Follow Neteon on LinkedIn for more edge AI fundamentals, or contact [email protected] and visit www.neteon.net for OPC-UA-ready edge platform datasheets.
FAQs
How is OPC-UA different from MQTT?
MQTT is a lightweight pub/sub transport with no built-in data model — every consumer needs out-of-band schema agreement. OPC-UA bundles transport, a typed information model, and security in one spec, and can itself run over MQTT (OPC-UA PubSub). For edge AI, that built-in semantics layer is the difference between a feature pipeline that survives a sensor change and one that doesn't.
Do I need TSN to run OPC-UA?
No. Standard OPC-UA over TCP works on any switched Ethernet. TSN becomes relevant when you need bounded latency for closed-loop AI control next to PLCs — typically sub-millisecond jitter. For monitoring and most inference use cases, a managed industrial switch with QoS such as the PLANET IGS-10020MT is sufficient.
Can a Neousys edge AI computer act as both an OPC-UA server and client?
Yes. Open62541 and Eclipse Milo both support running server and client roles in the same process. A common pattern on the Nuvo-11000 is to expose plant-aggregated tags as a server while subscribing to upstream OPC-UA endpoints from supervisory systems.
How many tags can an edge OPC-UA server handle?
On a Nuvo-11000 with Intel Core Ultra and 32 GB RAM, open62541 routinely handles 50,000+ nodes with sub-100 ms publish intervals on hundreds of subscriptions. Real-world ceilings depend more on certificate validation overhead and historian write paths than on the protocol itself.
Is OPC-UA secure enough for converged IT/OT networks?
OPC-UA's Sign+Encrypt security policies use X.509 certificates and AES-256, which meets IEC 62443 expectations. The weak link is usually certificate lifecycle management, not the protocol. Pair it with role-based access on the server and a TPM-backed certificate store on the edge node, both available on the Nuvo-11000.
For a complementary integration walkthrough, see our remote monitoring stack guide pairing the Nuvo-9160GC with a Teltonika cellular gateway and MQTT.
For how OPC-UA fits into a layered network design, see our converged IT/OT network architecture guide.